In 2025, more than 3.4 billion dollars in cryptocurrency was stolen in hacks, including a 1.5 billion dollar breach at Bybit that became one of the largest exchange compromises on record. At the same time, scams such as romance fraud, fake trading platforms, and investment schemes pulled in at least 14 billion dollars on‑chain, and updated estimates suggest total scam losses for 2025 will climb toward 17 billion dollars once more illicit wallets are identified. Chainalysis’ 2026 Crypto Crime Report shows that illicit addresses received at least 154 billion dollars in 2025, driven heavily by sanctioned entities and organized scam networks. If you are reading this, there is a good chance you have just joined these statistics.
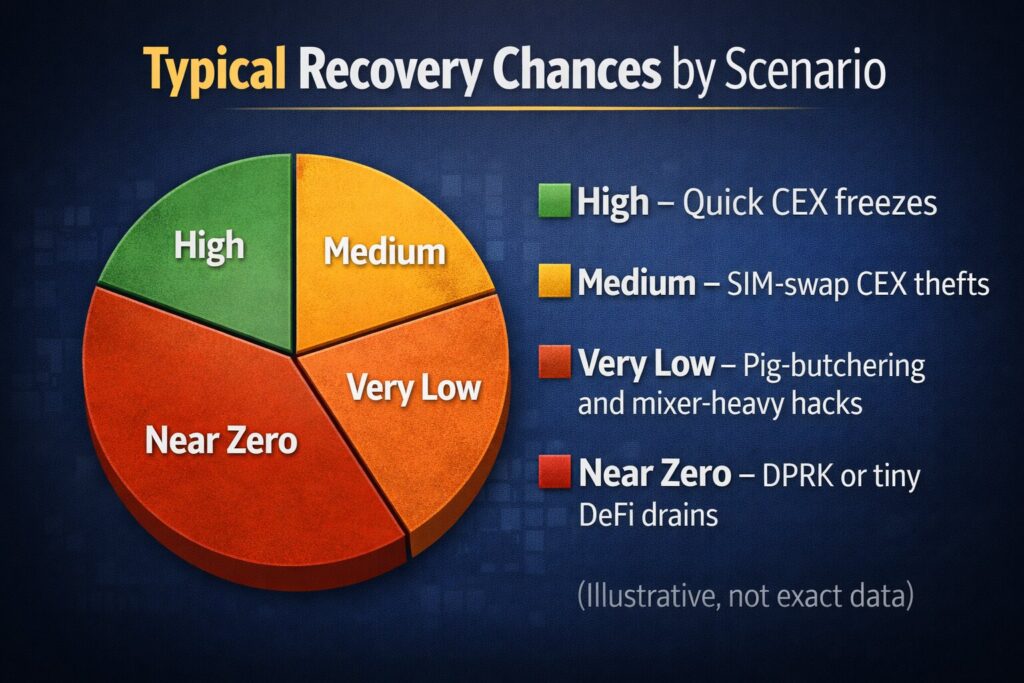
Here is the reality you need to hear, even though it hurts: in most single‑victim crypto theft cases, more than 90 percent of the money is never recovered. Funds move in seconds. Scammers sit in compounds in other countries. Some attacks are backed by nation‑states. On the surface, the game looks rigged against you. But that is not the full story. When victims act quickly, document everything, trace funds properly, and get the right people involved, real recoveries do happen. In 2025, the U.S. Secret Service, Tether, and Coinbase worked together to freeze and seize about 225 million dollars in USDT from a Southeast Asia pig‑butchering network, after Tether blacklisted 39 addresses and re‑issued the tokens to a wallet controlled by investigators. The U.S. Department of Justice (DOJ) has seized roughly 15 billion dollars in bitcoin tied to the Prince Group scam empire, with plans for victims to file claims. Federal agents in North Carolina seized nearly 8.5 million dollars in crypto from investment scams, while separate DOJ actions have frozen about 112 million dollars linked to pig‑butchering accounts in Arizona, California, and Idaho. In late 2025, prosecutors in Virginia used civil forfeiture to recover almost 1.7 million dollars in cryptocurrency and stablecoins for fraud victims.
You are not alone, and you are not powerless. This guide is written mainly for readers in the United States, because many of the most effective reporting channels and legal tools are U.S.‑based. But you can still use it if you live in another country. The early‑stage steps (securing your accounts, preserving evidence, basic tracing) are almost the same everywhere, and international operations such as the United Kingdom’s seizure of 61,000 bitcoin from a Chinese‑linked investment fraud show that courts around the world are now able to track, freeze, and eventually redistribute stolen crypto. North Carolina’s 61 million dollar USDT seizure, supported by Tether, is another sign that international cooperation is finally catching up with industrial‑scale scams.
You should also be clear about what this guide is not. It is not a magic script that guarantees you will get your coins back. No honest lawyer, investigator, or exchange can promise that. It is not an advert for “crypto recovery agents” in your DMs. Those services are almost always second‑stage scams that will steal even more money from you. Instead, this guide shows you the real, legitimate paths that have worked for other victims: securing what is left, building iron‑clad documentation, tracing your own funds with free tools, escalating correctly to authorities, pushing exchanges and stablecoin issuers to freeze assets, and, when it makes sense, hiring professionals who actuall.
The harsh truth – recovery odds, timeline & what affects success
2025–2026 numbers at a glance
These numbers tell you why the “default” outcome after a theft is permanent loss. Most scams are run by organized groups that move funds across chains, mixers, and foreign exchanges in minutes, and law enforcement has to focus on the largest and most serious cases first.
Factors that actually improve your odds
Your chances are not random. They go up a lot when a few key conditions are true:
-
Funds are still sitting at a centralized exchange (CEX) or in a stablecoin that can be frozen.
In the 225 million dollar pig‑butchering seizure, Tether froze 39 addresses, burned the stolen USDT, and re‑issued the same value to a wallet controlled by the U.S. Secret Service, after Coinbase and others helped trace the flows. -
You move in the first 24–72 hours.
In that same case, investigators ran a four‑day “sprint” once the pattern was understood, and stablecoins were frozen before all funds could be layered through mixers and off‑ramps. -
There is a KYC trail at regulated platforms.
Recent DOJ seizures in North Carolina, Arizona, and Virginia all depended on tracing on‑chain flows into accounts at exchanges and payment services, then using subpoenas and forfeiture actions to seize balances and return them to victims. -
The loss is large enough, or there are many victims.
In practice, agencies and serious law firms are more likely to prioritize cases when the loss is above 10,000–50,000 dollars, or when many people have been hit by the same scam and the total runs into the millions.
When recovery is almost impossible
There are situations where even world‑class tools and lawyers can do very little:
-
Funds sent straight into heavily used mixers or sanctioned services.
When attackers push your coins directly into tools like Tornado‑style mixers and then spread them over many hops, it becomes very hard to show that any later wallet “contains your money” in a legal sense. -
Nation‑state operations (for example, DPRK hacks).
North Korean hackers stole around 2.02 billion dollars in crypto in 2025 alone, often from exchanges and DeFi platforms, and they use long, complex laundering chains across many countries. Governments may seize some of this years later, but individual retail victims rarely see direct refunds. -
Very small amounts with no exchange touchpoint.
If a drainer took 200 dollars of tokens from a self‑custody wallet and instantly swapped and bridged them through DeFi, law enforcement is unlikely to open a full case.
Common types of crypto theft & tailored recovery feasibility
You improve your decisions when you match your situation to the right “playbook.” Here is a quick comparison of major scam and theft types.
This table is to guide your expectations, not to give legal advice. Every case is different.
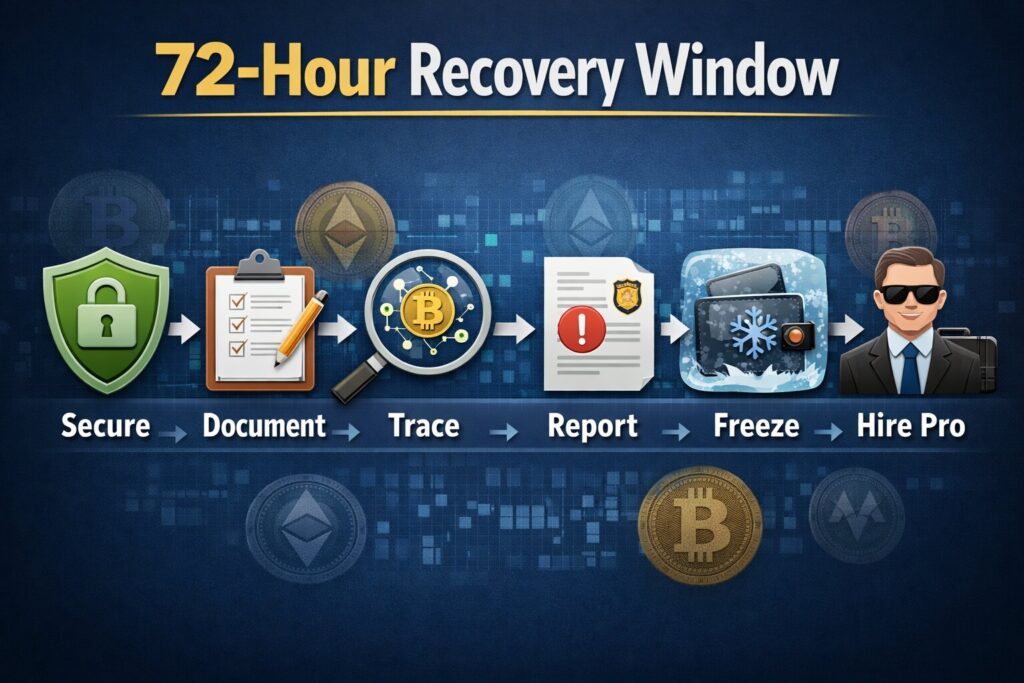
First 72 hours – exact action plan
The first 72 hours are your “critical window.” Your goal here is simple: stop further loss, lock in evidence, and create a clean trail that real investigators can use later.
0–15 minutes: stop the bleeding
-
Disconnect and calm down.
Put your phone in airplane mode if you suspect malware or remote control, and close all suspicious tabs or apps. Panic leads to bad clicks and more losses. -
Move any remaining funds.
-
If your seed phrase or recovery phrase is exposed, treat that wallet as dead. Move any remaining coins to a brand‑new wallet created on a different device with a new seed.
-
If only a single token was drained via an approval, use a token‑approval page (such as Etherscan’s “Token Approvals”) to revoke spending rights, then move your tokens after revocation.
-
-
Change all important passwords.
Update email, exchanges, cloud storage, password manager, and social media. Turn on unique, long passwords; use a password manager if you do not already. -
Upgrade your 2FA.
If you still use SMS codes, switch to app‑based codes (for example, Google Authenticator, Authy) or, even better, a hardware security key. SIM‑swap victims and lawyers who deal with these cases strongly recommend moving away from SMS 2FA.
15–60 minutes: document everything
-
Write a simple timeline.
Note when you first saw the problem, when the last “normal” login or transaction was, and when any strange messages or calls came in. -
Take screenshots.
Capture wallet balances “before and after,” scam websites, dashboards, login screens, exchange pages, and any chats with scammers or fake support. -
Copy raw data.
Make a text file with:-
transaction IDs (TxIDs)
-
your own wallet addresses
-
suspect addresses
-
exchange account IDs and ticket numbers
-
-
Back up your evidence.
Save copies to a secure cloud drive and an external disk so nothing is lost if a device crashes or needs to be wiped.
1–4 hours: trace the stolen funds and set alerts
-
Find the key TxIDs.
From your wallet or CEX export, identify each outgoing transaction that you did not authorize. -
Open those TxIDs in explorers.
Use Etherscan for Ethereum, Blockchain.com for Bitcoin, Solscan for Solana, or Blockchair for multi‑chain searches. -
Follow the money a few steps.
Click through to see where the stolen funds moved, at least three to five hops. Note if they land at a labeled exchange, bridge, or mixer. -
Set live alerts.
Create a free or trial account with Arkham or Nansen, add the leading scam wallets to a watchlist, and enable email or Telegram alerts. This tells you when funds move into or out of specific addresses.
4–24 hours: report and request freezes
-
Contact all exchanges the funds touched.
If any address is labeled as “Binance,” “Coinbase,” “OKX,” etc., open urgent tickets through their official sites only, explain the theft, attach TxIDs, and ask for a temporary freeze and investigation. -
File an FBI IC3 report (U.S.).
Go to ic3.gov and fill out the online form with: timeline, losses, TxIDs, addresses, website URLs, communication screenshots, and which exchanges are involved. FBI public guidance for crypto scam victims tells you to include exactly this level of detail. -
Report to the FTC and other regulators.
Use ReportFraud.ftc.gov to log your scam, which feeds into data used by many agencies tracking pig‑butchering and other frauds. If your scam involved fake investments or platforms, consider complaints to the SEC and CFTC as well. -
File a local police report.
Go to your local police or online reporting portal with your evidence file. Even if they cannot run a full cyber investigation, you will get a report number that exchanges, insurers, and courts often require later.
24–72 hours: bring in professionals
-
Talk to a crypto‑savvy lawyer.
Many U.S. law firms now specialize in SIM‑swap, pig‑butchering, and exchange‑related crypto thefts. A paid consult can tell you if arbitration, civil suits, or class actions are realistic in your case. -
Consider a blockchain forensics firm (for large losses).
Companies like Chainalysis, Elliptic, TRM Labs, and their partners maintain detailed maps of scam clusters, mixers, and exchange relationships. A professional report from them can carry more weight with big exchanges and law enforcement. -
Discuss legal tools and where to use them.
In the U.S., that might mean civil lawsuits or preparing claims in DOJ forfeiture cases. In countries like the U.K., lawyers can seek disclosure orders and worldwide freezing orders from high courts when you have enough tracing evidence.
What not to do
These mistakes destroy your chances and invite more scams:
-
Do not pay “recovery agents” who contact you first.
Fraud advisories and DOJ press releases warn that pig‑butchering networks often run fake “recovery” teams that demand upfront fees or “taxes” to release funds. -
Do not send more money to the scam platform.
Requests for extra deposits, unlock fees, or tax prepayments are a clear sign of a pig‑butchering or fake‑exchange scam. -
Do not lie or inflate your loss on reports.
If your case turns into a court matter or forfeiture claim, false statements will hurt you. -
Do not publicly accuse individuals without solid proof.
You could be sued for defamation and also tip off scammers before investigators act.
Step 1 – preserve iron‑clad evidence
Strong evidence is what separates “sorry, nothing we can do” from “we can move forward with this.” Build a single, clean case file from day one.
12‑item evidence checklist
-
Your ID documents – passport or national ID, plus proof of address.
-
Account ownership – screenshots or PDFs of exchanges showing your name, email, and balances.
-
Transaction records – CSV exports or statements for deposits, withdrawals, and trades covering at least three months around the incident.
-
Your own wallet addresses – list all addresses you control, labelled by wallet (MetaMask, Ledger, Phantom, etc.).
-
Stolen funds TxIDs and counterparties – for each unauthorized send, record TxID, sending address, receiving address, token, network, time, and value.
-
On‑chain tracing notes – a short explanation of how funds moved from your address to exchanges, mixers, or other clusters.
-
Scam communications – chat logs, emails, DMs, voice transcripts showing what the scammer promised and how they gained your trust.
-
Website evidence – URLs, WHOIS info if available, and screenshots of login pages or fake dashboards.
-
Security event logs – SMS from your carrier about SIM changes, unusual login alerts from email or exchanges, and password reset notices.
-
Support tickets – all messages with exchanges, wallet providers, and any “compliance” or “fraud” departments, plus case numbers.
-
Police and regulator reports – numbers from IC3, local police, FTC, SEC/CFTC, Action Fraud (UK), etc.
-
Personal impact statement – a short text on how much you lost, how it affects you, and how you were targeted; this is often used in victim restitution.
Simple template you can copy into Google Docs or Notion
Use these sections as headings:
-
1. Summary of the incident – what happened in 1–2 short paragraphs.
-
2. Timeline – bullet list with dates and times.
-
3. Assets and losses – table of coins/tokens, amounts, and approximate fiat value.
-
4. Transactions – table with TxIDs, from, to, token, network, and explorer links.
-
5. Communications – paste key chats or attach PDFs.
-
6. Reports filed – list all case numbers and the agencies.
-
7. Contacts – names and emails of officers, lawyers, and exchange staff.
You can build this in Docs or Notion and share a view‑only link with professionals later.
Step 2 – trace your stolen funds yourself
You do not need paid software to create a basic money trail. Free tools give you enough to understand what happened and to give investigators a head start.
Core free tools you can use
-
Block explorers – Etherscan (Ethereum), Blockchain.com (Bitcoin), Solscan (Solana), Blockchair (multi‑chain). These show transactions, token transfers, and sometimes labels like “Binance” or “Kraken.”
-
Arkham Intelligence – an analytics platform that labels many exchanges, funds, and some scam clusters, and lets you set alerts for specific addresses.
-
Nansen (free or trial plans) – a portfolio tracker with millions of labeled wallets (CEX, DeFi, whales) and notifications when tracked wallets move funds.
-
TRM Labs free wallet screening tool – lets you check if an address is linked to scams, sanctions, or other high‑risk activity.
-
Dune Analytics and public dashboards – community dashboards that follow major hacks, scam families, and mixer flows.
Step‑by‑step basic tracing
-
Start at your own transaction.
Paste the TxID of an unauthorized transaction into the right explorer (for example, Etherscan). -
Identify the “to” address.
Note the address that received your funds and check if the explorer labels it as an exchange, bridge, or known contract. -
Follow the next few hops.
Click into the receiving address and follow outgoing transactions. You are looking for:-
deposits into labeled CEX wallets
-
swaps into stablecoins (USDT, USDC)
-
interactions with bridges and mixers
-
-
Map it in a simple diagram.
Draw a basic flow: “My wallet → Address A → Binance hot wallet → Address B.” This is often enough to explain the path to non‑technical people. -
Screen high‑risk addresses.
Use TRM’s free screening tool to see if any of the wallets are already flagged as scam or sanctions‑linked. -
Add the key addresses to Arkham/Nansen.
Set up alerts so you see movement out of the main scam wallets, which can show which exchanges or services are being used next.
You do not have to be perfect here. Your goal is to make sure every important step in the money trail has at least a TxID and address you can hand to professionals.
Step 3 – report to authorities
You might feel like reporting is useless. It is not. The biggest recoveries in 2023–2026 happened because thousands of separate victims filed reports that helped agencies see patterns and hit the biggest scam clusters.
United States: who you should contact
-
FBI Internet Crime Complaint Center (IC3)
-
Website: ic3.gov – click “File a Complaint.”
-
Include: all TxIDs, amounts, dates, your addresses, scam addresses, exchange names, URLs, and a short timeline.
-
FBI crypto guidance specifically asks victims to provide transaction details, wallet addresses, and communication records.
-
-
Local police / sheriff
-
File a report in person or online.
-
Bring your evidence file and a simple one‑page summary.
-
Ask for a copy of the report and the case number.
-
-
Federal Trade Commission (FTC)
-
Website: ReportFraud.ftc.gov.
-
Choose categories like “Impostor scams” or “Investment scams” if it fits.
-
These reports feed into national databases for scam trends.
-
-
SEC, CFTC, and state securities regulators (for investment scams)
-
If you were pushed into “crypto investment products” or fake trading platforms, these may be unregistered securities or derivatives schemes.
-
The SEC has brought many crypto fraud cases and uses tip data for investigations.
-
-
U.S. Secret Service and Homeland Security task forces
-
The Secret Service has dedicated digital asset crime teams and helped seize the 225 million dollars in pig‑butchering funds.
-
Your IC3 or police report can be shared with them; in big cases, they may contact you later.
-
-
IRS (for tax angle)
-
If you lost funds, the IRS treats most stolen crypto differently from normal capital losses, but there are narrow cases where theft or casualty rules apply and may interact with future recoveries.
-
Talk to a tax professional before you claim anything.
-
International contacts
If you live outside the U.S., still do the steps above when your scam touched U.S. exchanges or U.S. dollar stablecoins, but also:
-
UK – Action Fraud and local police – the UK has handled some of the largest crypto seizures and victim redress programs.
-
EU member states – national cybercrime units – many countries have online fraud reporting sites that share data with Europol.
-
Interpol channels – often used by national police, not by individuals, but your local report can travel through these channels in big cases.
Sample short script you can adapt
“I am reporting a cryptocurrency theft / investment scam. On [date], I discovered unauthorized transactions from my wallet/exchange account. Between [dates], I sent a total of [amount and asset] to addresses provided by [describe scammer: ‘romance contact,’ ‘person claiming to be Coinbase support,’ etc.]. Attached are transaction IDs, wallet addresses, screenshots of the scam platform and communications, and records of my exchange accounts showing ownership and balances. I request that this information be used to investigate the scam and, if possible, support any asset seizure or victim restitution efforts.”
Always ask for a reference or complaint number and keep it in your evidence file.
Step 4 – notify exchanges & get freezes (works 40–60% of time if fast)
Centralized exchanges and stablecoin issuers are your best shot at a quick freeze. They will not act on every request, but they do freeze accounts and tokens when the case is clear and timely.
How to approach major exchanges
Use the official support pages only. Never search for “Coinbase support number” on Google; scammers buy ads for those. Go through the website or app.
Key points to include in your first message to any CEX (Coinbase, Binance, Kraken, Gemini, OKX, etc.):
-
A short subject line like: “URGENT: Stolen funds – request for account review and freeze.”
-
The exact TxIDs that sent funds into addresses the exchange controls.
-
Screenshots of the explorer page showing their deposit address receiving your funds.
-
Your police and IC3 report numbers if you already have them.
Example email template (you can adapt per exchange):
Subject: URGENT – Stolen funds involving your platform (TxIDs included)
Dear [Exchange] Compliance / Fraud Team,
I am a victim of a cryptocurrency theft/investment scam discovered on [date]. On‑chain analysis shows that part of my stolen funds were sent to deposit addresses controlled by your exchange.Key details:
– My address(es): [your addresses]
– TxIDs where funds left my control: [list TxIDs with explorer links]
– Addresses believed to be your deposit wallets: [list addresses with explorer links and labels]
– Total amount involved: [amount + asset, e.g., 5.2 BTC, 120,000 USDT]I have filed reports with law enforcement:
– FBI IC3 report number: [number, if in U.S.]
– Police report number: [number]
– Other agencies: [FTC/SEC, etc. if any]I respectfully request that you:
Review the above transactions and associated accounts for fraud.
Place a temporary restriction or enhanced monitoring on accounts holding the suspected funds where permitted by law and your policies.
Advise me and my investigating officer (if assigned) on any additional information you require.
I understand that you must follow your legal obligations and privacy policies and I am not asking for personal information of other customers without proper legal process. I only request that you take any steps available to prevent further dissipation of stolen funds and cooperate with law enforcement.
Sincerely,
[Your full name]
[Contact details]
Guides from specialist law firms note that when victims move quickly and provide clear TxIDs and case numbers, exchanges are much more likely to flag or freeze accounts while law enforcement requests formal information.
Stablecoin issuers: Tether (USDT) & Circle (USDC)
Tether and Circle can blacklist addresses and freeze tokens in some situations, especially when they receive requests from law enforcement:
-
Tether (USDT) – has repeatedly frozen USDT linked to hacks and pig‑butchering rings and has been publicly thanked by the DOJ for its role in a 61 million dollar pig‑butchering seizure.
-
Circle (USDC) – maintains terms that allow freezing or redeeming USDC balances on law‑enforcement request or for sanctions compliance.
You usually cannot get them to freeze funds with a victim email alone, but:
-
You can send them a short, factual incident description with TxIDs and case numbers.
-
This information can help when agencies reach out to them with formal requests later.
Real‑world data shows hundreds of addresses frozen by USDT and USDC issuers between 2023 and 2025, often at law enforcement request, including many linked to investment and pig‑butchering scams.
Step 5 – hire the right professionals
If your loss is large, you will be tempted to pay anyone who promises fast recovery. Most of those offers are scams. You need to know how to sort real help from predators.
Red flags: fake recovery companies (99% of the market)
Avoid any “recovery firm” that:
-
Contacts you first on social media, email, or SMS.
-
Promises guaranteed or “high‑probability” recovery.
-
Demands large upfront fees or “unlock” payments before they start.
-
Asks you to send them your seed phrase, passwords, or full remote access.
-
Has fake reviews, no real law licenses, and no verifiable case histories.
Regulators and victim‑support groups warn that pig‑butchering rings often recycle victims through fake recovery operations, squeezing them twice.
Legit options: who can actually help
-
Blockchain forensics firms and their partner networks
-
Chainalysis, Elliptic, TRM Labs, CipherTrace, and similar companies provide tracing reports used by exchanges and law enforcement.
-
Many do not sell directly to individuals, but work through law firms or specialist consultancies.
-
-
Crypto‑specialist law firms
-
Look for firms that:
-
publish case studies or blog posts about real seizures, SIM‑swap cases, and class actions;
-
name the courts and case numbers;
-
clearly list their lawyers and bar memberships.
-
-
They may help with: arbitration against exchanges, civil suits, Norwich Pharmacal and Bankers Trust orders (in the U.K. and similar systems), and claims in DOJ forfeiture cases.
-
-
Private investigators with crypto training
-
In some jurisdictions, licensed investigators work with lawyers and forensics providers to collect evidence and locate suspects’ real‑world assets.
-
Typical costs and expectations
-
Initial consults – often a flat fee or hourly rate to review your case.
-
Full tracing and litigation support – can reach thousands to tens of thousands of dollars, so it usually only makes sense for large losses.
-
No guarantees – a real professional will tell you clearly that recovery is uncertain and depends on many factors, especially speed and jurisdiction.
When in doubt, ask for references and published case names you can verify in court or regulator databases.
Step 6 – legal weapons that actually work in 2026
The legal side of crypto recovery has matured fast. Courts are now comfortable treating crypto as property and using old tools in new ways.
Civil tools
-
Norwich Pharmacal orders (NPOs)
-
Used mainly in common‑law countries like the U.K.
-
Force a third party (such as an exchange) to disclose information about wrongdoers so you can identify and sue them.
-
Courts have granted NPOs against crypto exchanges and even allowed service of legal documents via NFT airdrops in some cases.
-
-
Bankers Trust orders
-
Similar to NPOs but focused on getting information about where misappropriated assets went.
-
Have been granted against crypto exchanges to uncover fund flows so assets can be frozen or seized.
-
-
Worldwide freezing orders / proprietary injunctions
-
High courts in the U.K. and other jurisdictions have issued worldwide freezing orders over crypto assets to stop dissipation while a case is heard.
-
Often combined with disclosure orders so you can locate assets first.
-
These tools are powerful but expensive and usually worth it only for large losses or group actions.
Criminal and public tools
-
Criminal investigations and asset forfeiture
-
The DOJ and other agencies seize crypto in criminal and civil forfeiture actions, as in the 112 million dollar pig‑butchering seizure and the 15 billion dollar Prince Group case.
-
Victims can later file remission or restoration claims to get some of these funds back.
-
-
Private prosecutions (e.g., U.K.)
-
In some countries, victims can bring private criminal charges in addition to civil cases, though this is complex and must follow strict rules.
-
-
Class actions & group claims
-
When many victims are hit by the same platform or breach, class‑action lawsuits or representative actions may be used to negotiate compensation or share recovered funds.
-
Filing for restitution after a DOJ seizure (high level)
When DOJ seizes assets linked to investment or pig‑butchering schemes, they often:
-
Announce the seizure in a public press release, naming a case number and sometimes a website.
-
Later open a formal remission or restitution process where victims can:
-
submit proof of payments (TxIDs, bank wires);
-
show communications with scammers;
-
verify that their funds went into the seized wallets.
-
-
Review claims and distribute recovered funds proportionally after legal costs and priorities.
If your scam matches a seizure description, a good lawyer can help you prepare a strong claim.
Real success stories & case studies (2024–2026)
You need to see that real victims do sometimes get their money back, at least partly.
-
225M USDT pig‑butchering seizure – Tether, Coinbase, Secret Service
Tether froze 39 addresses linked to a Southeast Asia pig‑butchering ring, burned 225 million USDT, and re‑issued them to a wallet controlled by the U.S. Secret Service. Coinbase and others provided on‑chain analysis and victim identification support. -
15B bitcoin Prince Group seizure
The DOJ seized around 15 billion dollars in bitcoin tied to the Prince Group scam network linked to forced‑labor compounds in Cambodia and other countries. Victims of associated pig‑butchering schemes are expected to file claims over time. -
UK 61,000 BTC seizure
UK police seized about 61,000 BTC (worth around 7 billion dollars at the time of some reports) from a Chinese‑linked investment fraud, and authorities are now debating how to return value to victims. -
112M multi‑state pig‑butchering seizure (Arizona, California, Idaho)
The DOJ seized roughly 112 million dollars from accounts at U.S. banks and exchanges that were used to launder cryptocurrency scam proceeds. -
8.5M seizure in North Carolina
Federal agents in North Carolina seized nearly 8.5 million dollars in cryptocurrency tied to investment fraud schemes, with TRM Labs analysis supporting the tracing. -
1.7M recovery for U.S. victims in Virginia
The Eastern District of Virginia used civil forfeiture to recover nearly 1.7 million dollars in crypto and stablecoins for victims of overseas investment scams.
Behind every one of these numbers is a group of people who filed reports, saved TxIDs, and stayed engaged long enough to be included in victim lists. You can too.
Tax & accounting implications
This section is not tax advice. Always check with a crypto‑aware CPA or tax lawyer.
Reporting theft and losses
-
The IRS currently treats most crypto as property.
-
After the 2017 tax law changes, personal theft losses are generally not deductible, but there may be narrow exceptions for losses connected with a trade, business, or certain federally declared disasters.
-
Many tax guides now suggest you should still document your loss (date, amount, evidence) even if you do not claim a deduction, because it matters later when you recover funds.
If you later recover stolen crypto
When you get some or all of your stolen coins back, tax treatment can be tricky:
-
In many cases, the recovery is treated like getting back property you previously owned, and the later sale triggers capital gains or losses based on your original cost basis and holding period.
-
If you took any deduction earlier (for example, as a theft or casualty loss in a qualifying situation), part of the recovery may be taxable income rather than a non‑taxable return of capital.
Because the rules keep changing and enforcement is tightening, do not guess. Hand your tax professional your full incident timeline and all documents.
Bonus – how to never lose crypto again
You cannot control everything, but you can make yourself a very hard target. Think of this as a 12‑layer safety net.
12‑layer security checklist
-
Use hardware wallets (Ledger, Trezor, etc.) for long‑term holdings, not browser extensions.
-
Keep seed phrases offline, written on paper or metal, never in cloud notes or screenshots.
-
Use a separate “hot” wallet with small balances for daily DeFi or NFT use.
-
Turn on app‑based or hardware key 2FA for all exchanges and email accounts.
-
Lock your SIM with a PIN and ask your carrier to add a high‑risk note for SIM‑swap alerts.
-
Bookmark official exchange and wallet URLs; never click login links from email or DMs.
-
Before you connect a wallet to a new dApp, search its name with words like “scam,” “rug,” “exploit.”
-
Regularly revoke token approvals you no longer need using explorer tools.
-
Run basic malware and keylogger scans if your computer behaves strangely.
-
Treat any urgent message from “support” asking for codes or seed phrases as a scam. No real support staff need your seed.
-
Spread holdings across more than one exchange and wallet, and keep a written inventory.
-
Teach friends and family these basics; scammers love to hit people in your circle who trust you.
Scam‑spotting mini‑quiz
-
Would you trust a stranger who DMs you with “insider” crypto signals?
-
Would you ever share a seed phrase or 2FA code if someone says they are from support?
-
Does a “trading platform” ask you to pay “taxes” or “fees” before letting you withdraw?
If the answer should be “no,” but you feel tempted to say “yes,” you are already in the danger zone.
Frequently asked questions
1. Can the police actually recover my stolen Bitcoin?
Sometimes, yes. Police and agencies like the DOJ and Secret Service have recovered large amounts of bitcoin and stablecoins from pig‑butchering and investment scams, but they focus on big, organized cases, not every single theft.
2. How long does crypto recovery take?
Anything from days (for quick exchange freezes) to several years (for large international cases and forfeiture processes). Many victims never see funds again, but when they do, it is usually after long investigations and court proceedings.
3. Is my stolen USDT on Tron still traceable?
Yes. TRC‑20 USDT is on a public blockchain. Investigators can follow it just like ERC‑20 USDT, and Tether has frozen USDT on many chains when asked by law enforcement.
4. Do recovery companies that charge upfront fees work?
Legitimate firms may charge for real work like tracing and legal action, but anyone who guarantees results, cold‑contacts you, or demands large upfront payments with no proper contract is very likely a scam.
5. What if my crypto was stolen from a hardware wallet like Ledger or Trezor?
In most cases, the device itself was not hacked. Either the seed phrase was exposed, malware grabbed your seed, or you signed a malicious transaction. Recovery odds are similar to other self‑custody thefts and depend on where the funds went next.
6. Can exchanges refund me if my account was hacked?
Sometimes. It depends on their terms, how the hack happened, and whether you followed their security rules. Some cases go to arbitration or court when victims argue that security was inadequate.
7. Should I still report my case if I only lost a small amount?
Yes. Your report helps agencies see patterns and may link your loss to bigger operations. Even if you are unlikely to get money back, your data still matters.
8. Do mixers make recovery impossible?
They make it much harder, especially when used heavily and across chains, but not always impossible. Investigators sometimes break down mixer flows or catch funds when they surface at exchanges.
9. Will my bank help if I wired money for a crypto scam?
Banks can sometimes reverse recent transfers or flag recipient accounts, but once funds are fully settled or converted, your chances drop. Still, you should report fraud to your bank quickly and ask them to file their own reports.
10. Can I sue a crypto exchange for not protecting my account?
Maybe. This depends on the exchange’s terms, your own security practices, and local law. There have been lawsuits and class actions against exchanges over hacks and account takeovers.
11. Is it worth hiring a lawyer if I lost under 10,000 dollars?
Usually no, unless you are part of a group case. For smaller losses, focus on reporting, blocking future attacks, and tax documentation.
12. Are romance and pig‑butchering scams really that common?
Yes. “Pig‑butchering” has grown rapidly, with FBI and media reports showing huge increases in cases and losses.
13. What if the scammer was overseas?
Most are. That does not mean you should not report. Many big cases are transnational, and foreign arrests and seizures often start from domestic victim reports.
14. My wallet was drained but I never clicked anything weird. How?
Common causes include malware on your device, a reused or leaked seed, old approvals to malicious contracts, or fake browser extensions. A deep security check is essential.
15. Should I publicly post my TxIDs and story on social media?
You can, but be careful. It can attract fake recovery scammers. If you do, never share seeds, codes, or private data, and consider blurring some details.
16. Is all this different in 2026 compared to a few years ago?
Yes. Crime has scaled up with AI and industrial scam centers, but law enforcement and analytics tools are also far more capable now, as the 61,000 BTC and 15B bitcoin seizures show.
Conclusion
If your crypto has just been stolen, you are hurting, angry, and probably blaming yourself. You are not stupid and you are not alone. Sophisticated, industrial‑scale operations are designed to fool smart people at scale.
Your best move now is to treat this like an emergency and a legal case at the same time. In the next 72 hours, focus on three things: secure what is left, document everything in one place, and get your case into the systems that actually lead to freezes and seizures. After that, decide calmly whether the size of your loss justifies hiring professionals or joining group actions.
You cannot control whether your particular case ends up in the small slice of funds that are recovered. You can control how well you prepare, how quickly you act, and how safely you handle crypto from this day forward.